Your Outsourced Team Ships Fast. But Who’s Reviewing What They Leave Behind?
Huzefa Motiwala April 1, 2026
Your outsourced team might be delivering features quickly, but have you checked the code they’re leaving behind? Speed often comes at the cost of quality, and ignoring this can result in:
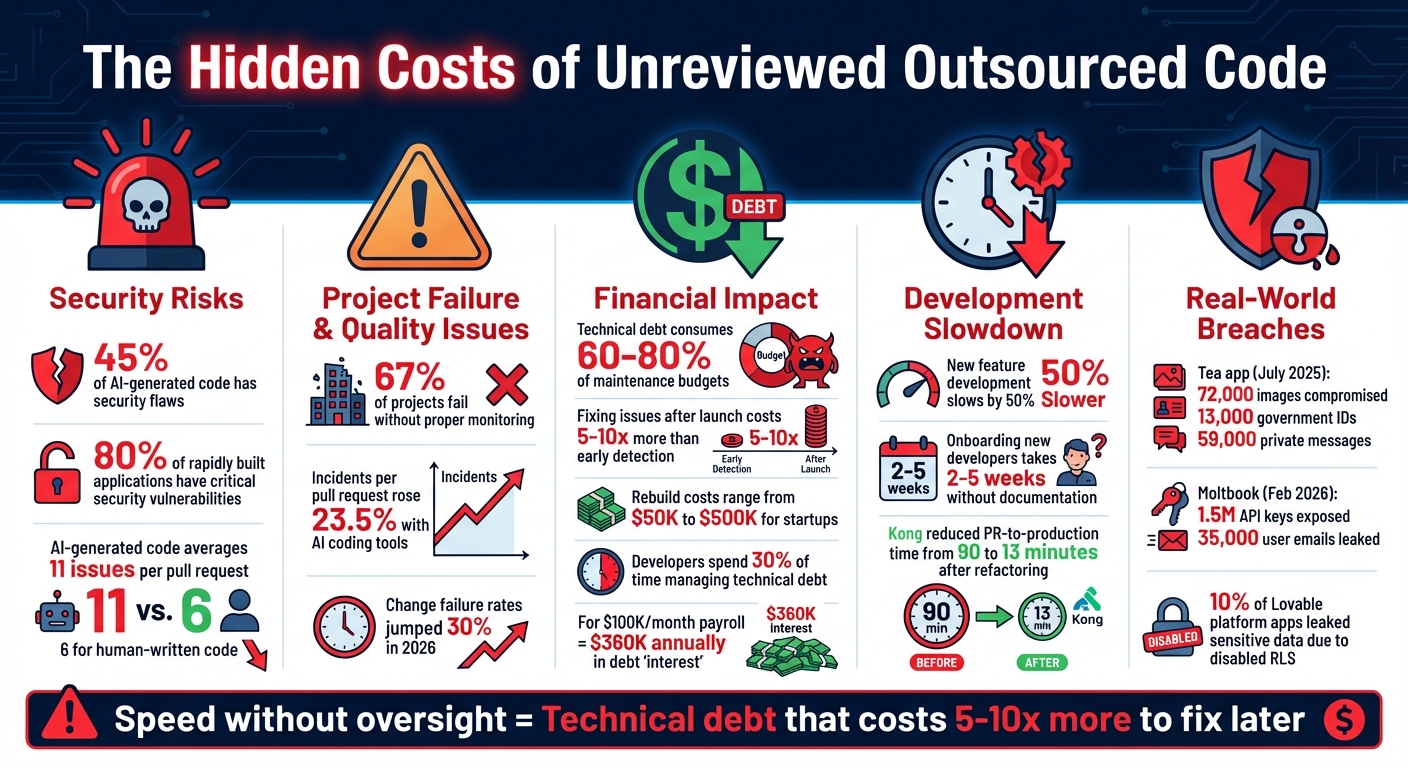
- Hidden vulnerabilities: 45% of AI-generated code has security flaws.
- Technical debt: It can consume 60–80% of your maintenance budget and slow future development.
- Fragile systems: Rushed code often fails to scale or breaks under heavy use.
- Knowledge gaps: Poor documentation makes onboarding and maintenance harder.
- Vendor lock-in: Lack of oversight can leave you dependent on external teams.
Real-world examples, like Moltbook’s database breach in 2026, show how unreviewed code can lead to costly failures. To protect your product, prioritize code reviews, expert audits, and structured handoffs. Use tools like AI scans and Traffic Light Reports to catch issues early, and ensure your internal team has the knowledge to maintain and grow your system. Don’t let speed today create problems tomorrow.
The Hidden Costs of Unreviewed Outsourced Code: Key Statistics
Code Reviews Are Broken? Here’s What AI Changed
sbb-itb-51b9a02
What Happens When Speed Comes Before Quality
When outsourced teams focus on speed over building solid foundations, the cracks might not show during initial demos. But over time, these hidden flaws can surface, threatening system reliability and stalling growth.
Fragile Systems That Break Under Load
Rushing to deliver often means sacrificing long-term resilience. Code that works fine for a handful of users can collapse when demand increases. Why? Rapid development often leads to tightly connected components, inefficient queries, and missing caching layers – shortcuts that only reveal their flaws under heavy traffic. In 2026, engineering teams using AI coding tools managed to produce 20% more pull requests, but this came at a cost: incidents per pull request rose by 23.5%, and change failure rates jumped 30% [3]. Greg T., a technical interviewer at Lemon.io, summed it up perfectly:
"Every shortcut taken today becomes a roadblock tomorrow" [6].
So, while a system might handle 1,000 users, scaling it to 10,000 could require a major overhaul. Prioritizing speed over quality may seem efficient, but it ultimately undermines the stability and scalability of the product.
Missing Documentation and Knowledge Gaps
Fast-paced development often skips thorough documentation, which can turn onboarding new developers into a drawn-out process lasting anywhere from two to five weeks [2]. Even worse, when teams move on, they leave behind a black hole of missing context. As the Boundev team aptly points out:
"The cost of poor documentation compounds faster than any other technical debt. Once documentation decays, every new hire becomes a potential point of failure" [7].
Combine these knowledge gaps with fragile code, and you’ve got a recipe for growth bottlenecks. Without careful oversight, these issues can snowball, derailing product stability and efficiency.
How Poor Code Quality Stops Growth
Neglecting code quality doesn’t just slow things down; it can jeopardize the entire product. A poorly configured Firebase instance, for example, once exposed tens of thousands of sensitive records [2]. Fixing such issues after launch can cost far more than addressing them during development. Take Enrichlead as a cautionary tale: the startup built its product entirely with AI under a "zero hand-written code" philosophy. But just days after launch, security researchers uncovered vulnerabilities that allowed unauthorized users to access paid features and modify data. The fallout forced the company to shut down [8].
When speed takes precedence over proper oversight, the result isn’t a reliable product – it’s a ticking time bomb. These examples highlight why rigorous code reviews are essential to ensure sustainable growth and protect against costly mistakes.
Why You Need Oversight for Outsourced Work
Outsourcing development without keeping a close eye on things can lead to a "Black Box" scenario. In this case, the vendor holds all the technical knowledge while you shoulder the risks. If your CTO can’t explain how the system functions without consulting the agency, you don’t truly own your code – you’re essentially renting it. This risk becomes apparent when project milestones are met on paper, but underlying issues remain hidden.
Completed Milestones That Hide Real Problems
A project might look on track, with a green Jira board signaling progress, but that doesn’t always tell the full story. Alarmingly, 67% of projects fail outright when proper monitoring is neglected [4]. While a project manager may report success, the codebase could be riddled with problems like hardcoded API keys, zero test coverage, or unresolved "TODO" comments.
One warning sign is the "Friday Dump" – when outsourced teams stay quiet all week and then flood the repository with 50+ commits late on Friday. This tactic can give the illusion of progress but undermines continuous integration practices, making proper code reviews nearly impossible.
Security vulnerabilities are another hidden danger. For instance, 80% of applications built using rapid AI generation (sometimes called "vibe coding") have critical security flaws [2]. A real-world example is the Tea dating app. In July 2025, the app seemed to hit all its milestones, but poor security oversight left its Firebase instance exposed. This breach compromised 72,000 images – including 13,000 government ID photos – and 59,000 private messages [2]. Ignoring these issues early on only deepens your reliance on the vendor later.
Getting Locked Into Vendor Relationships
Weak systems and undocumented code can lead to vendor lock-in, a situation where you become overly dependent on the vendor. They hold critical architectural knowledge, understand the workarounds, and are privy to undocumented decisions – leaving you at a disadvantage. This dependency makes switching teams or bringing development in-house both expensive and risky.
The financial impact of this is significant. Fixing issues after launch can cost 5–10 times more than addressing them early [2]. Startups that fail to oversee outsourced work often face rebuild costs ranging from $50,000 to $500,000 [2]. On top of that, vague contract terms – like "shared ownership" or "retained rights for reusable components" – could allow vendors to claim legal rights over your product’s core functionality, further limiting your control [5].
Unreviewed code also leads to mounting technical debt. This can consume 60–80% of your maintenance budget and slow new feature development by as much as 50% [2]. Without proper oversight, you’re not just risking your current project – you’re compromising your long-term growth.
How to Review and Fix Outsourced Code
When dealing with outsourced code, reviewing and refining it is a direct way to address hidden vulnerabilities and technical debt. Before scaling your system, hiring new developers, or continuing with your vendor, take a step back and assess your codebase’s overall health. Using audit methods can quickly reveal issues that manual reviews might miss. Once you have a clear understanding of the weaknesses, it’s time to use automated tools for a more detailed assessment.
AI-Agent Assessment and Traffic Light Reports
A hybrid approach is often the most effective: AI agents scan your codebase for vulnerabilities, while senior engineers bring in the business context and judgment that only experience can provide. This combination ensures every file is covered while prioritizing issues appropriately [9].
Here’s how it works: AI agents scan for vulnerabilities and patterns within 72 hours. Day 1 focuses on scanning, Day 2 is for expert validation, and Day 3 delivers a Traffic Light Roadmap. This roadmap classifies issues into three categories:
- Critical (Red): Immediate attention required, such as hardcoded API keys.
- Managed (Yellow): Technical debt that needs monitoring.
- Scale-Ready (Green): Components ready for production [9][2].
This system avoids the common pitfall of treating every issue as equally urgent, which can lead to analysis paralysis. AI scans are particularly good at identifying recurring vulnerabilities, such as inconsistent design patterns often found in outsourced code. A practical tip during code reviews is the "30-Second Rule": if a developer can’t explain a code block in 30 seconds, it likely needs refactoring [2].
For context, AI-generated code tends to have more issues compared to human-written code – averaging 11 issues per pull request versus 6 – and nearly half of it contains security flaws [1]. This makes thorough reviews essential.
Expert-Led Codebase Audits
While AI can identify patterns, it can’t determine if your architecture aligns with your business needs. That’s where expert-led audits come into play. A senior engineer or technical founder should review the system before any new work begins. The goal is to identify areas that need stabilization, determine what can be safely refactored, and establish proper handoff processes [9].
These audits go beyond surface-level syntax checks. They address questions like:
- Does the system use a modular structure that can scale?
- Is the database schema designed for future growth?
- Are configuration settings externalized properly? [9]
Security hygiene is another critical focus. For example, if your backend uses Supabase, make sure Row Level Security (RLS) is enabled. In May 2025, a scan of 1,645 apps built on the Lovable platform revealed that 10% of them leaked sensitive user data due to disabled RLS [2]. Similarly, tools like Socket.dev can help identify phantom dependencies – fake libraries suggested by AI that attackers might exploit [2].
Here’s a quick overview of common audit categories and red flags:
| Audit Category | Key Checks | Common Red Flags |
|---|---|---|
| Security | SQL injection, hardcoded secrets, auth bypass | API keys in Git, missing input sanitization |
| Performance | N+1 queries, missing indexes, memory leaks | DB queries inside loops, unindexed foreign keys |
| Architecture | Module coupling, circular dependencies | 2,000-line "utility" files, logic in UI components |
| Maintainability | Test coverage, naming consistency | Zero test coverage on payment logic, dead code |
Setting Up Structured Handoff Processes
Once expert audits confirm your architecture is stable, the next step is ensuring that knowledge is transferred effectively to your in-house team. Without proper documentation and handoff processes, even the most thorough review won’t be useful.
A structured handoff should include:
- The full repository
- Reproducible setup documentation
- Active credentials
- A runbook for routine tasks
- A final, verified version tag [10]
The real test of a successful handoff? Someone who didn’t build the app should be able to follow the documentation to build, run migrations, and deploy the product without relying on the original vendor [10].
Introduce a 24–72 hour code freeze before the handoff, allowing only urgent fixes. This ensures the codebase and running system remain in sync [10]. During this period, organize structured knowledge transfer sessions such as walkthroughs, pair programming, and Q&A workshops. These sessions capture the reasoning behind architectural decisions, not just the technical details [11]. Maintain Architectural Decision Records (ADRs) to document what decisions were made and why, so future developers don’t have to dig through commit history for context [12].
Finally, rotate all credentials immediately to remove unauthorized vendor access. This includes API keys, database passwords, and OAuth tokens. Audit and revoke the vendor’s access to production environments, cloud infrastructure, and third-party tools [12]. Without this step, vendors could retain backdoor access, posing security risks and creating unnecessary dependencies. Taking control of every credential is the final safeguard for your product’s stability and growth.
Managing Technical Debt as You Grow
As we move from identifying hidden code risks, it becomes clear that managing technical debt is essential as your business scales. Technical debt isn’t something you can completely avoid – it’s something you control with intention. The Variable-Velocity Engine (V2E) framework treats technical debt as a deliberate tool: you take it on to ship faster, then strategically pay it down at key business milestones. This method ensures your system remains functional during growth, preventing stagnation or chaos. Let’s dive into the transition from fast MVPs to scalable systems.
Moving from Fast MVPs to Scalable Systems
A disposable architecture helps you move quickly. It allows you to release an MVP, validate your market, and generate revenue at speed. But as your business gains traction, this architecture can start holding you back. That’s when Managed Architecture steps in – refactoring only the parts that block growth while keeping the functional components intact, avoiding a complete system overhaul.
The need to transition becomes obvious when tasks that used to take days now take weeks, or when system incidents become a regular occurrence. A great example of this shift is Kong, an API management company. In January 2024, they moved to a micro-frontend architecture to address scaling challenges. This change cut their PR-to-production time from 90 minutes to just 13 minutes and nearly doubled their weekly deployment frequency [2].
Paying Down Debt at Revenue Milestones
Refactoring becomes easier to justify when tied to revenue targets. If your system’s inefficiencies start slowing delivery or causing recurring problems, allocate resources to stabilize key components – like authentication systems or databases – once your budget allows.
A Delivery Impact Score can help you prioritize fixes. For instance, if features are consistently taking 50–100% longer than planned, the debt in that area is likely at a "High" severity level and needs immediate attention [14]. Technical debt can be expensive, too. Developers may spend up to 30% of their time managing it, which, for a company with a $100K/month payroll, translates to about $360K annually in "interest" [13]. Framing the issue in financial terms – such as explaining that "this module delays features by 2 weeks and cost $180K in engineering time last quarter" – can help leadership see the tangible impact [14].
Regular Reviews and Cross-Trained Teams
Once you’ve addressed the most pressing refactoring needs, regular reviews and cross-training can help maintain steady growth. Quarterly system reviews are a great way to catch potential problems early. These reviews should involve both engineering and business leadership to ensure technical upgrades align with revenue goals. Tools like an Impact-Effort matrix can highlight quick wins – high-impact fixes that require minimal effort – without derailing your broader roadmap [13][14].
Cross-training your team is another critical step. When only one developer fully understands a vital system, such as payment logic or deployment processes, you risk creating a single point of failure. To avoid this, implement structured pair programming rotations and host regular "Tech Talks" to ensure multiple team members are familiar with all critical components [6][7]. This approach safeguards your operations, even when outsourced developers leave.
"Technical debt is the delta between the current state of your system and the state it needs to be in to support your current and near-future business goals." – CodeIntelligently [14]
Protecting Your Product’s Future
To secure your product’s future, it’s crucial to go beyond quick wins and prioritize stability. Shipping features rapidly without proper oversight may work in the short term, but it often leads to systems that crumble under pressure later. An outsourced team that delivers features in days might also leave behind fragile architectures and security vulnerabilities, which can cost 5–10 times more to fix after launch [2].
Start by incorporating AI scans for every commit before production. Consider the example of Moltbook’s breach in February 2026, where a misconfigured RLS exposed 1.5 million API keys and 35,000 user email addresses [2]. This highlights why automated scans should be paired with expert audits – AI tools can catch many issues, but human insight is essential for identifying deeper vulnerabilities. To manage these findings effectively, use a Traffic Light Roadmap:
- Red: Critical security fixes requiring immediate action
- Yellow: Refactoring tasks that can be managed over time
- Green: Components ready to scale
This system ensures you address urgent risks without stalling development.
Technical debt and poor documentation, as discussed earlier, can stifle growth. To avoid this, implement robust oversight processes now. These efforts should align with structured handoffs and cross-training to maintain system stability over the long term.
Structured handoffs are vital for preventing knowledge loss when outsourcing ends. To achieve this, require comprehensive documentation, such as detailed specification files, centralized decision logs, and module-level READMEs. These resources should act as a single source of truth. Additionally, ensure your internal team is cross-trained on critical systems – like payment logic or deployment processes – so no single point of failure exists due to external dependencies.
The cost of skipping these precautions is tangible. Startups often face massive expenses to rebuild applications after critical architectural failures. Similarly, technical debt from poorly reviewed code can absorb 60–80% of maintenance budgets [2]. By embedding verification into your workflow now, you’ll build a system that scales reliably without succumbing to future challenges.
FAQs
What are the quickest red flags in outsourced code?
When reviewing outsourced code, there are a few warning signs that can quickly indicate potential problems:
- Inconsistent coding standards: Look for unclear variable names, duplicate logic, or mismatched conventions. These inconsistencies can make the code harder to understand and maintain.
- Security vulnerabilities: Watch out for things like hardcoded API keys or weak input validation. These issues can leave your system exposed to attacks.
- Poor architecture: Telltale signs include tightly coupled components or a lack of proper tests. This often points to systems that are fragile, difficult to scale, and prone to technical debt.
Catching these problems early is crucial for maintaining both the quality of the code and the reliability of your systems.
When should I run a codebase audit (and who should lead it)?
A codebase audit is essential when you notice problems with code quality, security, or architecture. It’s especially helpful early in development or when tackling technical debt. These audits are also critical before scaling your application or after spotting recurring issues, like inconsistent code or security vulnerabilities.
To get the most out of an audit, it should be led by someone with experience – like a senior developer or QA lead. Their expertise ensures the code meets proper standards and remains scalable and secure.
What should a proper vendor handoff include so we truly own the system?
When transitioning from a vendor, it’s crucial to ensure you have everything needed to run the system independently. This includes complete documentation and access. Make sure you receive:
- The repository, including deployment files and migration scripts.
- Step-by-step setup instructions.
- Access credentials for all relevant systems.
- A detailed runbook covering tasks like deployments, rollbacks, and backup management.
Additionally, confirm that you have full ownership of the codebase and control over infrastructure, secrets, and deployment processes. This safeguards your system’s stability and prevents unnecessary reliance on the vendor.
Related Blog Posts
- Why AI-Generated Code Costs More to Maintain Than Human-Written Code
- The AI Developer Productivity Trap: Why Your Team is Actually Slower Now
- You Can Audit 100K Lines of Code in 48 Hours Now. Here’s What Most Teams Get Wrong When They Try
- What Founders Get Wrong About Technical Due Diligence (And What VCs Should Actually Ask)



Leave a Reply