What Founders Get Wrong About Technical Due Diligence (And What VCs Should Actually Ask)
Huzefa Motiwala March 23, 2026
Technical due diligence (TDD) isn’t just about reviewing code – it’s about evaluating whether a startup’s systems can support its growth and align with business goals. Many founders misunderstand this process, focusing on polished demos or clean code while ignoring scalability, technical debt, or team readiness. Investors, on the other hand, often ask the wrong questions, relying on surface-level cues instead of digging into risks like fragile architecture or unmanaged dependencies.
Key Takeaways:
- Founders’ Common Mistakes: Treating TDD as a code review, underestimating the importance of technical debt, relying too much on documentation, ignoring third-party dependencies, and hiding problems from investors.
- What VCs Should Ask: Questions about architecture stability, technical debt management, team continuity, and dependency risks to assess scalability and operational readiness.
- Why It Matters: Poor TDD can lead to scaling failures, rising costs, and loss of investor confidence, potentially derailing funding rounds or growth plans.
The best approach? Transparency about challenges and a clear plan to address them. Investors value judgment and readiness over perfection.
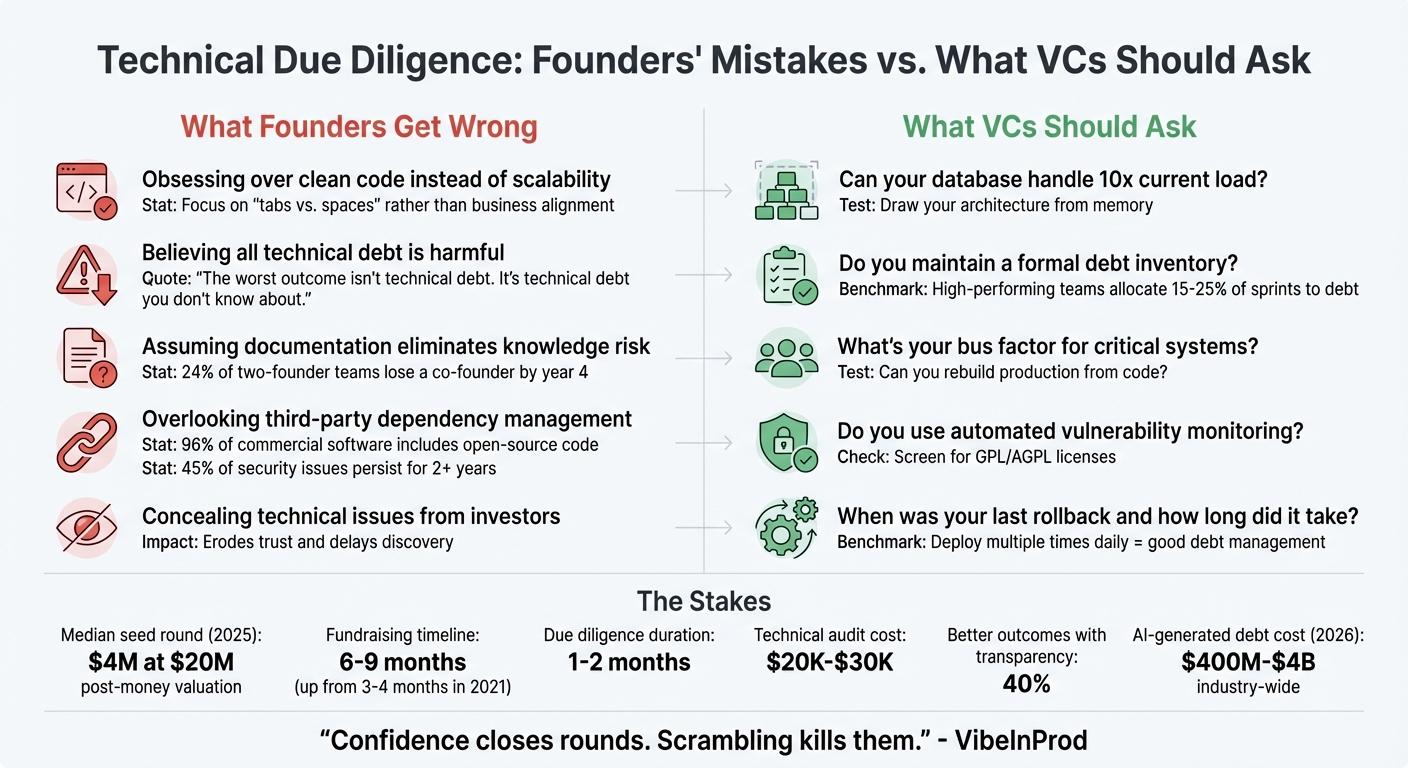
Founders’ Mistakes vs. What VCs Should Ask in Technical Due Diligence
Investor-Ready: Tech Due Diligence Strategies for Startups | LegalVision Australia
sbb-itb-51b9a02
What Founders Get Wrong About Technical Due Diligence
A common misstep founders make during technical due diligence (TDD) is treating it like a simple code review. They focus on polishing demos and tidying up files, but investors are assessing far more than functionality – they’re evaluating scalability and operational readiness [1]. This misunderstanding often leads to deeper issues.
Eliseo Robles, CTO of NurivaTech, refers to this as the "happy path" fallacy. Founders present polished demos, but investors want to see how systems handle failures, edge cases, and stress. As Robles puts it:
"Demos are theater. Decks are marketing. Code is truth." [6]
With AI coding tools enabling faster development, a working demo no longer guarantees robust technical foundations. Investors actively screen for "fragile foundations" because AI-generated systems can fail abruptly when scaled or pivoted [5].
Another issue is timing. In 2025, the median seed round hit $4 million with a $20 million post-money valuation [8]. With so much at stake, TDD now starts as early as pre-seed rounds, not just Series A [5]. Founders unprepared for this often scramble, which erodes investor confidence. As VibeInProd warns:
"Confidence closes rounds. Scrambling kills them." [5]
The consequences of these misconceptions are real. Misunderstanding TDD can stall deals, lead to pulled term sheets, or result in technical debt being used to negotiate down valuations [1][8]. Considering fundraising can take six to nine months, with diligence alone lasting one to two months [8], founders can’t afford these mistakes.
Mistake #1: Thinking TDD Only Checks Code Quality
Many founders obsess over clean code – debating "tabs vs. spaces" – when investors care about much bigger questions. TDD evaluates maintainability, scalability, and alignment between technical decisions and business goals [5][1].
For example, if a founder promises 10x growth, investors will check if the architecture can handle that scale. It’s less about elegance and more about "onboardability" – how quickly a new engineer can contribute to the codebase [5][1].
Expectations also depend on the company’s stage. A monolithic architecture at pre-seed isn’t alarming, but sticking with it at Series A without a plan for evolution signals trouble. Investors expect technical maturity to match the funding level and growth trajectory. Without scalable architecture, even the cleanest code can falter under growth.
Mistake #2: Believing All Technical Debt is Harmful
Technical debt often gets a bad rap, but investors know it’s inevitable – and sometimes strategic. The real problem isn’t having debt; it’s being unaware of it or unable to explain the trade-offs [3][1].
Startups accumulate debt intentionally to validate product-market fit before investing in perfect infrastructure. What’s concerning is when founders can’t articulate their decisions or plans to address the debt.
"The worst outcome isn’t technical debt. It’s technical debt you don’t know about." [5]
While debt can be strategic, poor documentation or lack of awareness about it creates risks that worry investors.
Mistake #3: Assuming Documentation Eliminates Knowledge Risk
Many founders think detailed documentation solves the "bus factor" problem – what happens if a key team member leaves. But documentation alone can’t eliminate knowledge risk because it can’t capture every nuance [3].
For example, Life Imaging’s platform lacked infrastructure documentation, leaving one person as the sole knowledge holder. Even with documentation, the absence of team-wide understanding created a critical risk [7]. As Matt Van Itallie, CEO of Sema, explains:
"The single most important factor for a codebase to clear TDD is if the developers who have created or maintained the code are still active at the company." [3]
Statistics show that 24% of two-founder teams lose a co-founder by year four [8]. When that happens, onboarding a new hire to understand a complex codebase can take months, delaying progress. Investors value team continuity over documentation because the people who built the system are irreplaceable in the short term.
Even documentation has its limits. Ganesh Kompella of Kompella Technologies notes:
"Documentation older than 12 months is often more dangerous than no documentation because it’s confidently wrong." [7]
Instead of relying solely on documentation, focus on onboarding velocity – how quickly a new senior engineer can contribute. If it takes more than four weeks, your system likely has too much implicit knowledge and inadequate documentation [7].
Mistake #4: Ignoring Third-Party Dependency Management
Many founders overlook how closely investors examine third-party dependencies. Around 96% of commercial software includes some open-source code, making dependency management a universal concern [3].
Investors use automated tools to audit dependencies for outdated packages or known vulnerabilities (CVEs). In one study, 95% of flagged security issues had been in the codebase for six months or more, with 45% persisting for over two years [3]. This shows a lack of active technical health management.
There’s also legal risk. Open-source code with "CopyLeft" licenses, like GPL, may require you to release proprietary code for free [7][3]. If your codebase has GPL contamination, it can derail deals. Founders need to audit their dependencies to ensure proper licensing for commercial use [7].
AI coding tools can worsen this problem by recommending outdated or abandoned libraries. If you’re using AI for development, you must stay vigilant about dependency hygiene.
Mistake #5: Hiding Technical Problems from Investors
Trying to hide technical issues damages trust. Transparency, on the other hand, builds it. Investors aren’t looking for perfection – they’re looking for sound judgment. When you acknowledge technical gaps and present a plan to address them, it shows self-awareness and operational readiness [5]. This reassures investors that you understand your system’s limitations and can allocate resources wisely.
Eliseo Robles sums it up:
"Technical due diligence that relies on non-technical signals isn’t due diligence. It’s theater." [6]
If founders conceal problems, investors are forced to rely on surface-level evaluations, which benefits no one. Hidden technical debt will eventually surface – either during diligence or post-investment, when it’s far costlier to fix.
A simple "weekend cleanup" can address many issues: remove hardcoded secrets, update dependencies, and create a basic README and deployment guide [5][1]. But the most impactful step is creating a technical debt register – a prioritized list of known issues. This signals that you’re not only aware of your challenges but also actively managing them.
Questions VCs Should Ask During Technical Due Diligence
Investors need smart, targeted questions to gauge whether a startup’s technical foundation can support its growth. Beyond spotting hidden technical debt or communication gaps, these questions dig into the company’s technical maturity. As Ganesh Kompella puts it:
"Architecture tells you more about a company’s technical maturity than any other signal." [7]
The following questions help investors evaluate whether a startup can scale, adapt, and maintain its systems over time. They focus on understanding how teams approach trade-offs – not just what they’ve built – bridging the gap between polished demos and operational readiness.
How to Evaluate Architecture Stability
A solid architecture reveals both current capabilities and future scalability. Start with the "draw the diagram" test: ask the engineering team to sketch their architecture from memory. If they can’t do so without referencing documentation, the system may be overly complex and hard to maintain [7].
Follow this up by asking whether their database schema can handle 10x the current load without requiring major refactoring [9]. Every system has its limits, and teams should be able to pinpoint potential bottlenecks, whether it’s a single-threaded process, an unsharded database, or API rate limits [7]. If they can’t identify these, they may not have stress-tested their architecture thoroughly.
Use the "last change" test to assess how tightly coupled their services are. Ask about the most recent cross-service change they implemented [7]. If it took more than a week to coordinate, their services might be too intertwined. Also, check if critical workflows rely on asynchronous job queues with proper monitoring and dead letter queues to handle traffic spikes [9]. Inquire about their API versioning and deprecation policies – without these, business model changes could disrupt integrations [9][7]. Lastly, confirm that the system supports horizontal scaling and that they aren’t relying on frameworks nearing their end-of-life within the next 18 months [9][7].
For startups centered on AI, ask how they validate and refactor AI-generated code to avoid duplicated patterns [5].
How to Assess Codebase Health and Technical Debt
The quality of the codebase and how technical debt is managed directly affect a startup’s ability to scale efficiently. Instead of asking if they have technical debt (because they almost certainly do), ask if they maintain a formal inventory of it. This inventory should categorize debt by severity, effort required to resolve, and its impact on the business [9].
Ask technical leads which part of the system they’d rebuild if they could, and check if high deployment velocity suggests effective debt management [4]. Teams that can deploy small changes multiple times a day are usually managing debt well [4]. On the other hand, infrequent deployments or those requiring significant coordination may signal a complex codebase.
See if they allocate part of their engineering roadmap to maintenance and debt remediation, not just new features [3][11]. Request Architecture Decision Records (ADRs) to understand why certain shortcuts were taken [1][4]. Review their Git history and pull request patterns [4]. Confirm whether regular architectural reviews are conducted or if code is merged without thorough scrutiny. Additionally, assess the "bus factor" for critical parts of the codebase – if only one person understands a key module, this creates a retention risk [1][3]. Finally, analyze incident logs and commit histories to see how the team performs under pressure [4].
How to Measure Team Continuity and Capability
A strong team is just as important as a strong codebase. Investors should verify that critical knowledge isn’t siloed with a single person. Ask how responsibilities are divided to ensure that the loss of one team member doesn’t jeopardize key integrations or infrastructure [14]. For instance, check whether systems like payments or billing are understood by more than one individual [1][3].
Ask if their production environment can be fully rebuilt from code [7]. Manual server configurations indicate operational risk. Explore their Infrastructure as Code (IaC) practices and whether failover mechanisms for critical components – such as the main API server or Redis – are documented and tested [9].
To gauge operational readiness, ask if they use blue-green deployments, canary releases, or feature toggles to reduce risk [10]. Also, inquire about their rollback process – when was the last rollback, and how long did it take? Teams that haven’t practiced rollbacks may struggle during failures. For more advanced teams, ask if they use chaos engineering practices (like Chaos Monkey) to test system resilience proactively [10].
How to Review Third-Party Dependencies and Security
Third-party dependencies and security practices provide insight into how well a team manages external risks. Confirm if they use tools like Dependabot or Snyk in their CI/CD pipeline for continuous vulnerability monitoring [10].
Ask if they’ve screened for restrictive licenses, like AGPL or GPL, which could pose legal challenges [12][10].
For system reliability, check if they’ve implemented redundancy, failover mechanisms, and circuit breakers in their microservices architecture [10]. A single dependency failure shouldn’t trigger a system-wide crash. Review material contracts for "change of control" clauses or termination risks that could cut off access to essential software [13]. Lastly, confirm they have a disaster recovery strategy in place for system shutdowns or breaches, and ensure that all domain names and email providers are registered under the company’s name [13].
What Happens When Technical Due Diligence Fails
When technical due diligence falls short, the consequences often emerge later as scaling challenges, ballooning expenses, and eroded investor confidence. Here’s a closer look at how these failures can manifest.
Scaling Failures from Weak Architecture
Poor architectural decisions early on can limit a company’s ability to grow. A system that works fine for 1,000 users might collapse under the weight of 10,000 users if it wasn’t built to handle larger loads. Common culprits include single-threaded processes, unsharded databases, and workflows that should operate asynchronously but don’t [7].
AI-generated code can further aggravate these problems. Tools like Cursor and Claude tend to prioritize quick solutions, often relying on basic patterns like synchronous, inline processing. While these approaches may work temporarily, they can cause systems to fail completely under traffic surges instead of degrading gradually [5]. Projects built with minimal oversight, often referred to as "vibe coding", might look good in demos but become unmanageable as the business scales [15].
The financial impact of these architectural flaws is immediate and severe. If a startup spends more than 15–20% of its Annual Recurring Revenue (ARR) on cloud infrastructure, it’s often a sign of scaling problems or inefficiencies [7]. Shared databases, a common shortcut in early-stage development, can turn into expensive liabilities later. For example, when Life Imaging’s platform was reviewed in February 2026, it was processing 10TB of radiology data daily. However, the lack of documentation for its infrastructure created a "bus factor of one" risk – meaning the entire system depended on the knowledge of a single individual [7].
These missteps not only hinder growth but also pile up technical debt, leading to rising costs.
Rising Costs from Unmanaged Technical Debt
Technical debt, if left unchecked, can spiral out of control. In extreme cases, it forces companies to rebuild their entire codebase, a process that can take months and drain financial resources [15][1]. By 2026, the estimated cost of addressing AI-generated technical debt across the industry ranged from $400 million to $4 billion. Thousands of startups required either complete rebuilds or "rescue engineering" due to unreviewed AI-generated code [15].
Ignoring technical debt also slows development. High-performing engineering teams typically dedicate 15–25% of their sprint cycles to managing this debt, ensuring consistent deployment speeds [18]. Without this focus, deployment cycles can stretch from hours to weeks. Even minor bug fixes may demand extensive coordination across fragile systems [4]. One fintech startup found that 38% of its failed deployments were tied to a single outdated payment module. Additionally, code duplication – a frequent issue in AI-generated codebases – made maintenance costly, as a single logic update often required changes across dozens of nearly identical functions [18][5].
Loss of Investor Confidence and Funding Opportunities
Failing to address technical debt during due diligence can destroy investor trust. It signals deeper problems, such as a lack of strategic planning or insufficient technical leadership. Dave Berardi from AKF Partners puts it plainly:
"The lack of a clear remediation plan suggests that the company either lacks the strategic foresight to prioritize technical debt or doesn’t have the technical leadership to execute complex refactoring projects." [17]
Technical issues can be deal-breakers. If the cost of rebuilding exceeds the capital invested, investors may lower valuations or pull out altogether [1][7]. Security flaws, like missing encryption, can also derail acquisition deals on the spot [7][1]. A notable example of asset mismanagement occurred with TWG Tea, which discovered in 2012 that its domain name was registered under a co-founder’s name. This oversight led to a seven-year legal battle before the domain was recovered in 2019 [16].
The expectations around technical due diligence are evolving. Once reserved for Series A funding rounds, thorough reviews are now common even at pre-seed and seed stages. Investors are shifting away from superficial evaluations and hiring external teams to conduct in-depth code reviews [6]. These changes highlight how critical technical due diligence is for a startup’s success and why neglecting it can derail even the most promising ventures.
Conclusion
Technical due diligence works best when founders and investors join forces to uncover genuine risks [2]. The real challenge lies in the disconnect between what executives present and the day-to-day realities engineers face. As Eliseo Robles, CTO at NurivaTech, aptly states:
"The gap between [the narrative and reality] is your actual risk" [6].
Prioritizing transparency over chasing perfection fosters trust more effectively. Founders who document challenges and maintain open communication with their teams experience 40% better outcomes during due diligence than those who attempt to obscure issues [2]. Acknowledging technical debt isn’t a sign of failure – it’s a reflection of founder judgment and an understanding of the choices made to reach this stage [1]. This honesty lays the groundwork for building systems that can scale and endure.
The goal isn’t to achieve a perfect codebase but to create a system designed for sustainable growth. Matt Van Itallie, Founder and CEO of Sema, highlights the broader responsibility:
"Codebase health is driven by the entire organization, not just engineering" [3].
Often, poor technical health stems from pressures in sales or finance rather than purely engineering shortcomings.
Identifying potential issues early can prevent costly mistakes. A thorough technical audit typically costs between $20,000 and $30,000 – a modest expense compared to the size of a Series A investment [6]. With fundraising timelines now stretching to 6–9 months (a significant increase from the 3–4 months common in 2021), getting technical systems in order from the outset has never been more critical [8].
FAQs
What should I prepare for technical due diligence before fundraising?
To get ready for technical due diligence, prioritize areas like scalable system architecture, codebase quality, and DevOps readiness. Make sure your documentation is thorough, your test coverage is solid, and robust security measures are in place. Be prepared to discuss your team’s skills, how you handle potential risks, and how your systems are designed to support growth. Careful attention to these aspects will showcase your technical strength and help you confidently navigate the process.
How can I prove my architecture will handle 10x growth?
To prove your architecture is ready for 10x growth, focus on showcasing its ability to scale effectively without introducing significant risks or costs. Start by emphasizing system stability – ensure your infrastructure can handle increased loads without compromising performance. Next, highlight modularity, which allows individual components to be upgraded or expanded independently, reducing disruption.
Capacity planning is another critical element. Demonstrate that you’ve analyzed current usage patterns and projected future needs to avoid over- or under-provisioning. Pinpoint the smallest changes required to enable growth, such as upgrading specific hardware, optimizing code, or leveraging cloud resources. Lastly, ensure the design supports seamless expansion – this means scaling up or out should not impact reliability or user experience.
What technical debt evidence do investors actually want to see?
Investors pay close attention to the health of a startup’s codebase, zeroing in on areas like maintainability, security, and potential hidden problems that could lead to expensive repairs after funding. They’re less interested in superficial metrics and more focused on understanding how scalable the system is and how well the company manages technical debt. Showcasing clear, proactive strategies to tackle these risks can signal technical maturity and a strong foundation for scaling.
Related Blog Posts
- Choosing the Right Outsourced Development Partner in India: Key Questions for Non-Tech Founders
- Technical Interviews Are Broken: What We Do Instead to Find Real Talent
- Every Startup Has Tech Debt. The Ones That Die Are the Ones That Pretend They Don’t.
- We Audited 5 Vibe-Coded Startups. Every Single Codebase Had the Same 3 Problems.




Leave a Reply